What this is
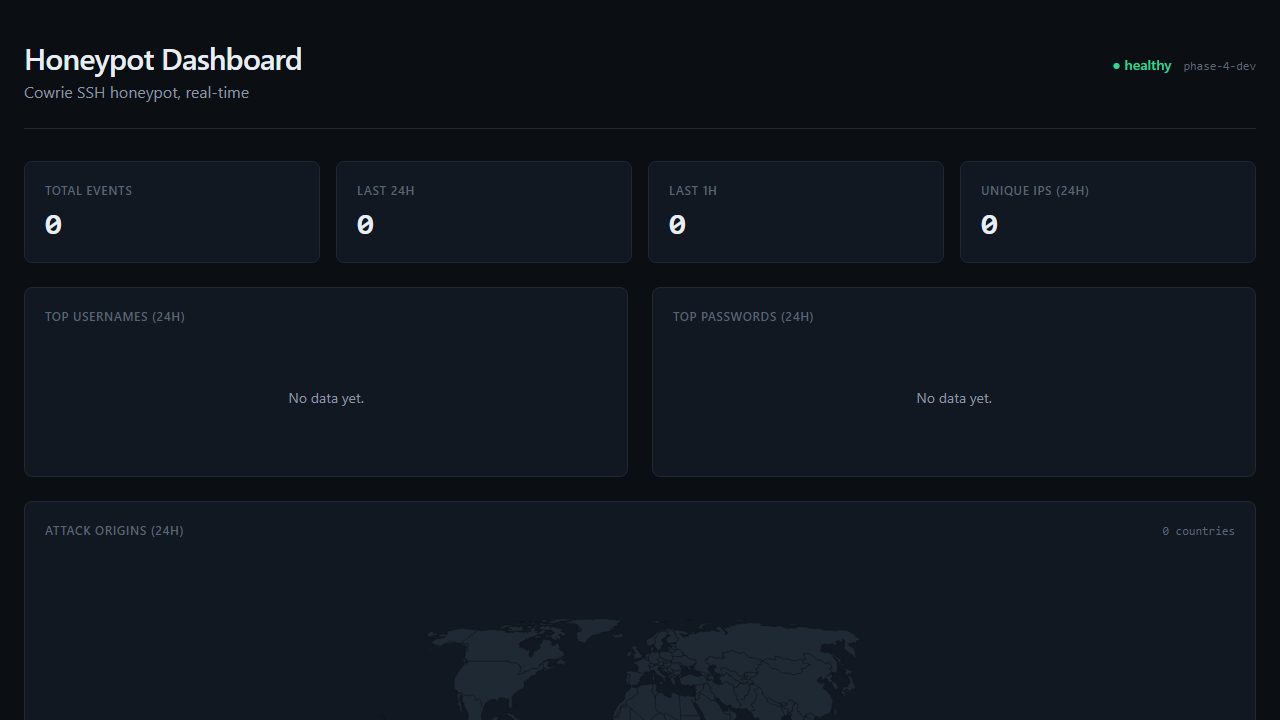
An SSH honeypot's traffic, plumbed end-to-end on AWS.
A Cowrie SSH honeypot accepts every login attempt the public internet throws at it and records the username, the password, the source IP, the timing, and any post-login activity. Honeypots see attacker traffic almost exclusively — most legitimate users never hit one — so the data is unusually clean signal.
The pipeline ships those events as gzipped JSON to S3. A Python Lambda validates each event with a strict Pydantic schema, classifies passwords against a bundled known-bad dictionary (ADR-005), attaches GeoIP enrichment, and writes a single-table DynamoDB row. A second Lambda consumes DynamoDB Streams to produce SUMMARY and RANK rollups idempotently.
A read-only API Lambda serves a TypeScript-strict React + Recharts SPA over CloudFront, behind Cloudflare's free WAF (ADR-007). The whole stack is Terraformed and runs at ~$2.60/month.